FW1060
- 0关注
- 1收藏,978浏览
最佳答案
您好,V7防火墙没这个命令。。。,v7配置命令变了
参考配置
1 配置需求及说明
1.1 适用的产品系列
本案例适用于软件平台为Comware V7系列防火墙:F100-X-G2、F1000-X-G2、F100-X-WiNet、F1000-AK、F10X0等。
1.2 配置需求及实现的效果
用户需求两台V7防火墙使用IKEV2协议对接IPSEC VPN,IP地址及接口规划如下表所示:
|
公司名称 |
外网接口 |
公网地址/掩码 |
公网网关 |
内网接口 |
内网地址/掩码 |
|
总部 |
0/0 |
1.1.1.1/24 |
1.1.1.2 |
0/1 |
9.9.9.0/24 |
|
分部 |
0/0 |
2.2.2.1/24 |
2.2.2.2 |
0/1 |
8.8.8.0/24 |
2 组网图
3 配置步骤
3.1 两端防火墙上网配置
防火墙上网配置请参考“2.3.2 防火墙外网使用固定IP地址上网配置方法”进行配置,本文只针对IPSEC VPN配置进行介绍。
3.2 总部侧创建IPSEC兴趣流匹配到分部的数据
创建IPSEC的感兴趣流,用于匹配IPSEC数据。
<H3C>system
[H3C]acl advanced 3000
[H3C-acl-ipv4-adv-3000]rule permit ip source 9.9.9.0 0.0.0.255 destination 8.8.8.0 0.0.0.255
[H3C-acl-ipv4-adv-3000]quit
创建acl 3001调用在外网接口用于排除IPSEC兴趣流不做NAT。
[H3C]acl advanced 3001
[H3C-acl-ipv4-adv-3001]rule deny ip source 9.9.9.0 0.0.0.255 destination 8.8.8.0 0.0.0.255
[H3C-acl-ipv4-adv-3001]rule permit ip source any
[H3C-acl-ipv4-adv-3001]quit
3.3 总部侧创建IPSEC安全提议
加密类型设置为3des-cbc,认证类型设置为md5。
[H3C]ipsec transform-set 1
[H3C-ipsec-transform-set-1] esp encryption-algorithm 3des-cbc
[H3C-ipsec-transform-set-1] esp authentication-algorithm md5
[H3C-ipsec-transform-set-1] quit
3.4 总部侧创建IKEV2安全提议
设备存在默认的IKE V2安全提议,所以不需要配置也存在参数。
[H3C]ikev2 proposal 1
[H3C-ikev2-proposal-1]quit
以下为IKE V2默认的加密及认证算法。
<H3C>display ikev2 proposal
IKEv2 proposal : default
Encryption: AES-CBC-128 3DES-CBC
Integrity: SHA1 MD5
PRF: SHA1 MD5
DH Group: MODP1536/Group5 MODP1024/Group2
3.5 总部侧创建IKE V2安全密钥
创建IKE V2密钥,地址填写分部侧设备的公网IP,密码设置为123。
[H3C]ike keychainv2 1
[H3C-ike-keychainv2-1-peer2]peer 2
[H3C-ike-keychainv2-1-peer2] address 2.2.2.1 255.255.255.255
[H3C-ike-keychainv2-1-peer2] identity address 2.2.2.1
[H3C-ike-keychainv2-1-peer2] pre-shared-key plaintext 123
[H3C-ike-keychainv2-1-peer2]quit
3.6 总部侧创建IKE安全框架
创建IKE安全框架,将对端地址、keychain、proposal关联起来。
[H3C]ikev2 profile 1
[H3C-ikev2-profile-1]keychain 1
[H3C-ikev2-profile-1] authentication-method local pre-share
[H3C-ikev2-profile-1] authentication-method remote pre-share
[H3C-ikev2-profile-1] match remote identity address 2.2.2.1 255.255.255.255
[H3C-ikev2-profile-1]quit
3.7 总部侧创建IPSEC安全策略
创建IKE安全策略GE0/0将transform-set、acl、ikev2-profile、对端地址关联起来。
[H3C]ipsec policy GE0/0 1 isakmp
[H3C-ipsec-policy-isakmp- GE0/0-1]transform-set 1
[H3C-ipsec-policy-isakmp- GE0/0-1]security acl 3000
[H3C-ipsec-policy-isakmp- GE0/0-1]remote-address 2.2.2.1
[H3C-ipsec-policy-isakmp- GE0/0-1]ikev2-profile 1
[H3C-ipsec-policy-isakmp- GE0/0-1]quit
3.8 总部侧在外网接口调用NAT及IPSEC策略
[H3C]interface GigabitEthernet 0/0
[H3C-GigabitEthernet 0/0]ipsec apply policy GE0/0
[H3C-GigabitEthernet 0/0]nat outbound 3001
[H3C-GigabitEthernet 0/0]quit
3.9 分部侧创建IPSEC兴趣流匹配到分部的数据
创建IPSEC的感兴趣流,用于匹配IPSEC数据。
<H3C>system
[H3C]acl advanced 3000
[H3C-acl-ipv4-adv-3000]rule permit ip source 8.8.8.0 0.0.0.255 destination 9.9.9.0 0.0.0.255
[H3C-acl-ipv4-adv-3000]quit
创建acl 3001调用在外网接口用于排除IPSEC兴趣流不做NAT。
[H3C]acl advanced 3001
[H3C-acl-ipv4-adv-3001]rule deny ip source 8.8.8.0 0.0.0.255 destination 9.9.9.0 0.0.0.255
[H3C-acl-ipv4-adv-3001]rule permit ip source any
[H3C-acl-ipv4-adv-3001]quit
3.10 分部侧创建IPSEC安全提议
加密类型设置为3des-cbc,认证类型设置为md5。
[H3C]ipsec transform-set 1
[H3C-ipsec-transform-set-1] esp encryption-algorithm 3des-cbc
[H3C-ipsec-transform-set-1] esp authentication-algorithm md5
[H3C-ipsec-transform-set-1] quit
3.11 分部侧创建IKEV2安全提议
设备存在默认的IKE V2安全提议,所以不需要配置也存在参数。
[H3C]ikev2 proposal 1
[H3C-ikev2-proposal-1]quit
以下为IKE V2默认的加密及认证算法。
<H3C>display ikev2 proposal
IKEv2 proposal : default
Encryption: AES-CBC-128 3DES-CBC
Integrity: SHA1 MD5
PRF: SHA1 MD5
DH Group: MODP1536/Group5 MODP1024/Group2
3.12 分部侧创建IKE V2安全密钥
创建IKE V2密钥,地址填写分部侧设备的公网IP,密码设置为123。
[H3C]ike keychainv2 1
[H3C-ike-keychainv2-1-peer1]peer 1
[H3C-ike-keychainv2-1-peer1] address 1.1.1.1 255.255.255.255
[H3C-ike-keychainv2-1-peer1] identity address 1.1.1.1
[H3C-ike-keychainv2-1-peer1] pre-shared-key plaintext 123
[H3C-ike-keychainv2-1-peer1]quit
3.13 分部侧创建IKE安全框架
创建IKE安全框架,将本端地址、对端地址、keychain、proposal关联起来。
[H3C]ikev2 profile 1
[H3C-ikev2-profile-1]keychain 1
[H3C-ikev2-profile-1] authentication-method local pre-share
[H3C-ikev2-profile-1] authentication-method remote pre-share
[H3C-ikev2-profile-1] match remote identity address 1.1.1.1 255.255.255.255
[H3C-ikev2-profile-1]quit
3.14 分部创建IPSEC安全策略
创建IKE安全策略GE0/0将transform-set、acl、ikev2-profile、对端地址关联起来。
[H3C]ipsec policy GE0/0 1 isakmp
[H3C-ipsec-policy-isakmp- GE0/0-1]transform-set 1
[H3C-ipsec-policy-isakmp- GE0/0-1]security acl 3000
[H3C-ipsec-policy-isakmp- GE0/0-1]remote-address 1.1.1.1
[H3C-ipsec-policy-isakmp- GE0/0-1]ikev2-profile 1
[H3C-ipsec-policy-isakmp- GE0/0-1]quit
3.15 分部侧在外网接口调用NAT及IPSEC策略
[H3C]interface GigabitEthernet 0/0
[H3C-GigabitEthernet 0/0]ipsec apply policy GE0/0
[H3C-GigabitEthernet 0/0]nat outbound 3001
[H3C-GigabitEthernet 0/0]quit
3.16 保存配置
[H3C]quit
3.17 隧道验证
通过如下显示信息查看到总部上IKEv2协商成功后生成的IKEv2 SA。
[H3C] display ikev2 sa
Tunnel ID Local Remote Status
--------------------------------------------------------------
1 1.1.1.1/500 2.2.2.1/500 EST
通过命令行查看dis ipsec sa可以看到隧道状态已经建立完成。
<H3C>dis ipsec sa
-------------------------------
Interface: GigabitEthernet0/0
-------------------------------
-----------------------------
IPsec policy: 1
Sequence number: 1
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1444
Tunnel:
local address: 1.1.1.1
remote address: 2.2.2.1
Flow:
sour addr: 9.9.9.9/255.255.255.255 port: 0 protocol: ip
dest addr: 8.8.8.8/255.255.255.255 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 2831964167 (0xa8cc5807)
Connection ID: 12884901889
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/1475
Max received sequence-number: 4
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 662015886 (0x27758f8e)
Connection ID: 55834574848
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/1475
Max sent sequence-number: 4
UDP encapsulation used for NAT traversal: N
Status: Active
通过如下显示信息查看到分部上IKEv2协商成功后生成的IKEv2 SA。
[H3C] display ikev2 sa
Tunnel ID Local Remote Status
--------------------------------------------------------------
1 2.2.2.1/500 1.1.1.1/500 EST
通过命令行查看dis ipsec sa可以看到隧道状态已经建立完成。
<H3C>dis ipse sa
-------------------------------
Interface: GigabitEthernet0/0
-------------------------------
-----------------------------
IPsec policy: 1
Sequence number: 1
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1444
Tunnel:
local address: 2.2.2.1
remote address: 1.1.1.1
Flow:
sour addr: 8.8.8.8/255.255.255.255 port: 0 protocol: ip
dest addr: 9.9.9.9/255.255.255.255 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 662015886 (0x27758f8e)
Connection ID: 12884901889
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/1431
Max received sequence-number: 4
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 2831964167 (0xa8cc5807)
Connection ID: 12884901888
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/1431
Max sent sequence-number: 4
UDP encapsulation used for NAT traversal: N
Status: Active
- 2021-08-10回答
- 评论(0)
- 举报
-
(0)
以下是F1060部署IPSEC VPN的举例,请参考:
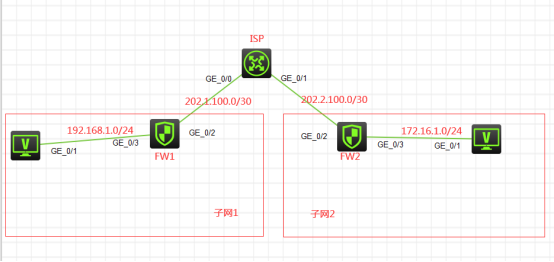
组网说明:
本案例采用H3C HCL模拟器的F1060防火墙来模拟IPSEC+IKE预共享密钥的典型组网配置。在网络拓扑图中存在子网1和子网2.为了保障子网1和子网2相互传输数据的安全性,因此需要在FW1与FW2采用IKE预共享的方式建立IPSEC VPN隧道。
配置步骤
配置思路:
1、按照网络拓扑图正确配置IP地址
2、FW1与FW2的互联接口加入安全域,并放通域间策略
3、FW1与FW2建立IPSEC VPN隧道,采用IKE预共享的方式
配置关键点
ISP:
System View: return to User View with Ctrl+Z.
[H3C]sysname ISP
[ISP]int gi 0/0
[ISP-GigabitEthernet0/0]des
[ISP-GigabitEthernet0/0]ip address 202.1.100.1 30
[ISP-GigabitEthernet0/0]quit
[ISP]int gi 0/1
[ISP-GigabitEthernet0/1]des
[ISP-GigabitEthernet0/1]ip address 202.2.100.1 30
[ISP-GigabitEthernet0/1]quit
[ISP]ip route-static 192.168.1.0 255.255.255.0 202.1.100.2
[ISP]ip route-static 172.16.1.0 255.255.255.0 202.2.100.2
FW1:
System View: return to User View with Ctrl+Z.
[H3C]sysname FW1
[FW1]int gi 1/0/3
[FW1-GigabitEthernet1/0/3]ip address 192.168.1.1 24
[FW1-GigabitEthernet1/0/3]quit
[FW1]int gi 1/0/2
[FW1-GigabitEthernet1/0/2]des
[FW1-GigabitEthernet1/0/2]ip address 202.1.100.2 30
[FW1-GigabitEthernet1/0/2]quit
[FW1]ip route-static 0.0.0.0 0.0.0.0 202.1.100.1
[FW1]security-zone name Trust
[FW1-security-zone-Trust]import interface GigabitEthernet 1/0/3
[FW1-security-zone-Trust]quit
[FW1]security-zone name Untrust
[FW1-security-zone-Untrust]import interface GigabitEthernet 1/0/2
[FW1-security-zone-Untrust]quit
[FW1]zone-pair security source trust destination untrust
[FW1-zone-pair-security-Trust-Untrust]packet-filter 2001
[FW1-zone-pair-security-Trust-Untrust]quit
[FW1]
[FW1]zone-pair security source untrust destination trust
[FW1-zone-pair-security-Untrust-Trust]packet-filter 2001
[FW1-zone-pair-security-Untrust-Trust]quit
[FW1]
[FW1]zone-pair security source trust destination local
[FW1-zone-pair-security-Trust-Local]packet-filter 2001
[FW1-zone-pair-security-Trust-Local]quit
[FW1]
[FW1]zone-pair security source local destination trust
[FW1-zone-pair-security-Local-Trust]packet-filter 2001
[FW1-zone-pair-security-Local-Trust]quit
[FW1]
[FW1]zone-pair security source untrust destination local
[FW1-zone-pair-security-Untrust-Local]packet-filter 2001
[FW1-zone-pair-security-Untrust-Local]quit
[FW1]
[FW1]zone-pair security source local destination untrust
[FW1-zone-pair-security-Local-Untrust]packet-filter 2001
[FW1-zone-pair-security-Local-Untrust]quit
FW1 IPSEC+IKE预共享密钥 关键配置点:
[FW1]acl advanced 3000
[FW1-acl-ipv4-adv-3000]rule 0 permit ip source 192.168.1.0 0.0.0.255 destination 172.16.1.0 0.0.0.255
[FW1-acl-ipv4-adv-3000]quit
[FW1]ike keychain james
[FW1-ike-keychain-james]pre-shared-key address 202.2.100.2 255.255.255.252 key simple james
[FW1-ike-keychain-james]quit
[FW1]ike proposal 1
[FW1-ike-proposal-1]quit
[FW1]ike profile james
[FW1-ike-profile-james]keychain james
[FW1-ike-profile-james]proposal 1
[FW1-ike-profile-james]match remote identity address 202.2.100.2 255.255.255.252
[FW1-ike-profile-james]quit
[FW1]ipsec transform-set james
[FW1-ipsec-transform-set-james]protocol esp
[FW1-ipsec-transform-set-james]encapsulation-mode tunnel
[FW1-ipsec-transform-set-james]esp authentication-algorithm md5
[FW1-ipsec-transform-set-james]esp encryption-algorithm des-cbc
[FW1-ipsec-transform-set-james]quit
[FW1]ipsec policy james 1 isakmp
[FW1-ipsec-policy-isakmp-james-1]security acl 3000
[FW1-ipsec-policy-isakmp-james-1]transform-set james
[FW1-ipsec-policy-isakmp-james-1]ike-profile james
[FW1-ipsec-policy-isakmp-james-1]remote-address 202.2.100.2
[FW1-ipsec-policy-isakmp-james-1]quit
[FW1]int gi 1/0/2
[FW1-GigabitEthernet1/0/2]ipsec apply policy james
[FW1-GigabitEthernet1/0/2]quit
FW2:
System View: return to User View with Ctrl+Z.
[FW2]int gi 1/0/3
[FW2-GigabitEthernet1/0/3]ip address 172.16.1.1 24
[FW2-GigabitEthernet1/0/3]quit
[FW2]int gi 1/0/2
[FW2-GigabitEthernet1/0/2]des
[FW2-GigabitEthernet1/0/2]ip address 202.2.100.2 30
[FW2-GigabitEthernet1/0/2]quit
[FW2]ip route-static 0.0.0.0 0.0.0.0 202.2.100.1
[FW2]security-zone name Trust
[FW2-security-zone-Trust]import interface GigabitEthernet 1/0/3
[FW2-security-zone-Trust]quit
[FW2]security-zone name Untrust
[FW2-security-zone-Untrust]import interface GigabitEthernet 1/0/2
[FW2-security-zone-Untrust]quit
[FW2]acl basic 2001
[FW2-acl-ipv4-basic-2001]rule 0 permit source any
[FW2-acl-ipv4-basic-2001]quit
[FW2]
[FW2]zone-pair security source trust destination untrust
[FW2-zone-pair-security-Trust-Untrust]packet-filter 2001
[FW2-zone-pair-security-Trust-Untrust]quit
[FW2]
[FW2]zone-pair security source untrust destination trust
[FW2-zone-pair-security-Untrust-Trust]packet-filter 2001
[FW2-zone-pair-security-Untrust-Trust]quit
[FW2]
[FW2]zone-pair security source trust destination local
[FW2-zone-pair-security-Trust-Local]packet-filter 2001
[FW2-zone-pair-security-Trust-Local]quit
[FW2]
[FW2]zone-pair security source local destination trust
[FW2-zone-pair-security-Local-Trust]packet-filter 2001
[FW2-zone-pair-security-Local-Trust]quit
[FW2]
[FW2]zone-pair security source untrust destination local
[FW2-zone-pair-security-Untrust-Local]packet-filter 2001
[FW2-zone-pair-security-Untrust-Local]quit
[FW2]
[FW2]zone-pair security source local destination untrust
[FW2-zone-pair-security-Local-Untrust]packet-filter 2001
[FW2-zone-pair-security-Local-Untrust]quit
FW2 IPSEC+IKE预共享密钥 关键配置点:
[FW2]acl advanced 3000
[FW2-acl-ipv4-adv-3000]rule 0 permit ip source 172.16.1.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
[FW2-acl-ipv4-adv-3000]quit
[FW2]ike keychain james
[FW2-ike-keychain-james]pre-shared-key address 202.1.100.2 255.255.255.252 key simple james
[FW2-ike-keychain-james]quit
[FW2]ike proposal 1
[FW2-ike-proposal-1]quit
[FW2]ike profile james
[FW2-ike-profile-james]keychain james
[FW2-ike-profile-james]proposal 1
[FW2-ike-profile-james]match remote identity address 202.1.100.2 255.255.255.252
[FW2-ike-profile-james]quit
[FW2]ipsec transform-set james
[FW2-ipsec-transform-set-james]protocol esp
[FW2-ipsec-transform-set-james]encapsulation-mode tunnel
[FW2-ipsec-transform-set-james]esp authentication-algorithm md5
[FW2-ipsec-transform-set-james]esp encryption-algorithm des-cbc
[FW2-ipsec-transform-set-james]quit
[FW2]ipsec policy james 1 isakmp
[FW2-ipsec-policy-isakmp-james-1]security acl 3000
[FW2-ipsec-policy-isakmp-james-1]ike-profile james
[FW2-ipsec-policy-isakmp-james-1]transform-set james
[FW2-ipsec-policy-isakmp-james-1]remote-address 202.1.100.2
[FW2-ipsec-policy-isakmp-james-1]quit
[FW2]int gi 1/0/2
[FW2-GigabitEthernet1/0/2]ipsec apply policy james
[FW2-GigabitEthernet1/0/2]quit
测试:
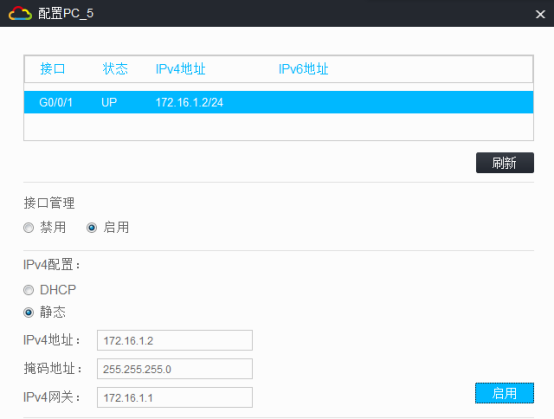
物理机都填写IP地址:

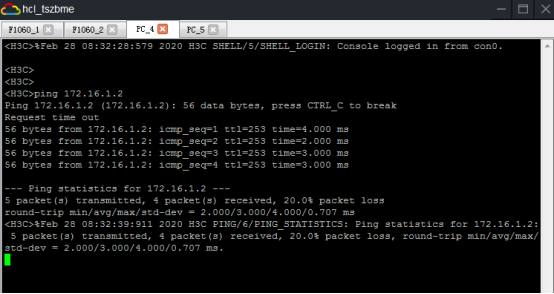
PC之间可以相互PING通:

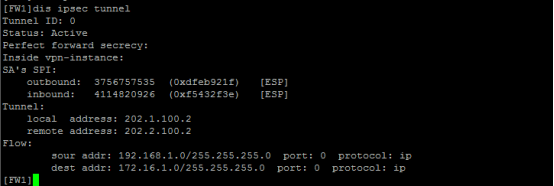
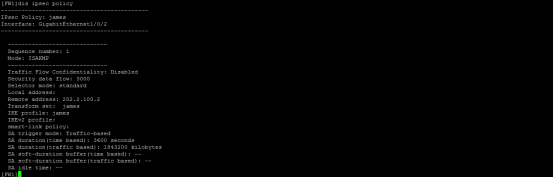
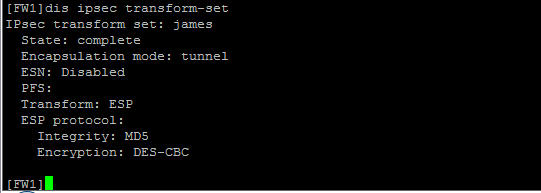
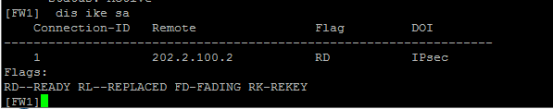
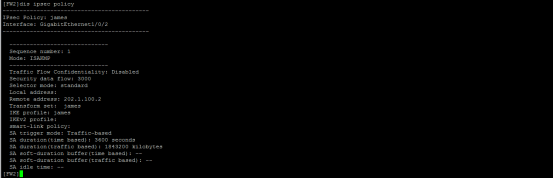
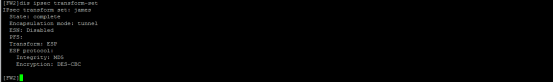
查看FW1的IPSEC显示信息:

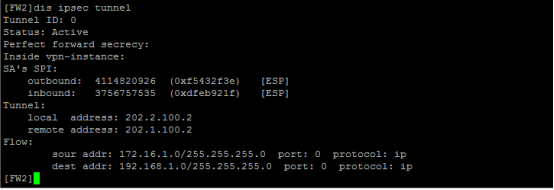
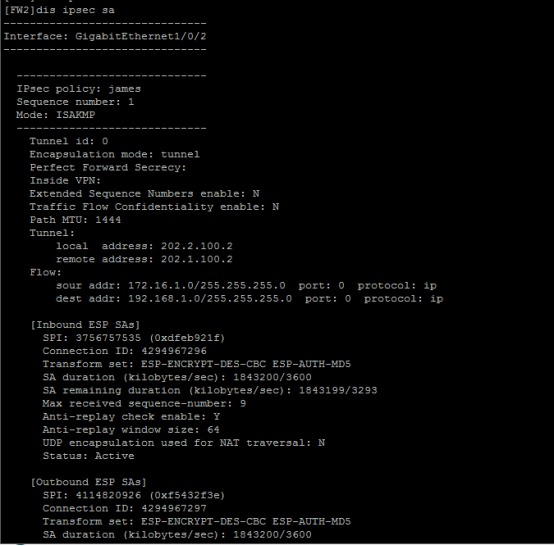
查看FW2的IPSEC显示信息:

- 2021-08-10回答
- 评论(0)
- 举报
-
(0)
暂无评论
编辑答案

亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明




暂无评论